As you prepare to take some time off to enjoy with your families (especially if a certain health crisis kept the festivities to a minimum in 2020) it’s important to take some steps to make sure your business is still protected in your absence.
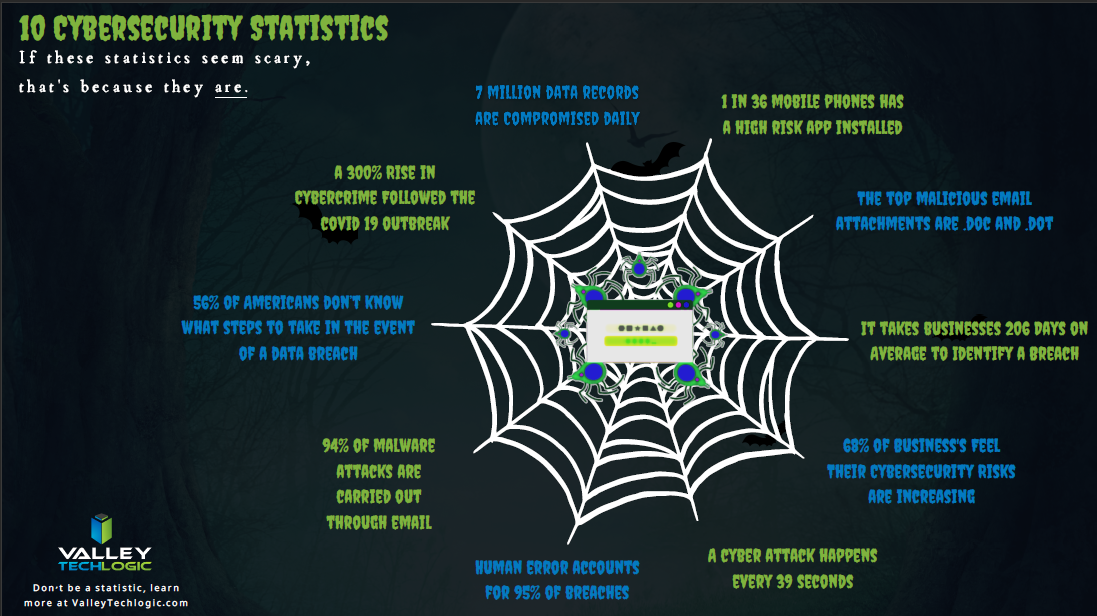
The Cybersecurity and Infrastructure Security Agency (CISA) issued an advisory yesterday to businesses and consumers alike, warning that hackers often take advantages of holidays and other times people may let their guard down to wreak more havoc.
The advisory included a warning of a possible increase on the following cyber threat events:
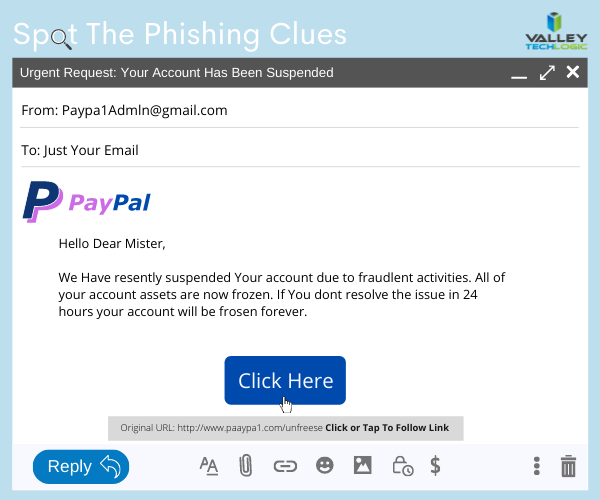
- Phishing attacks: That email from your Aunt Beth seeing if you’re going to bring the green bean casserole with a “Google Form” to check it off may not be what it seems to be.
- Fraudulent site spoofing: Especially for sites that may be seeing increased traffic due to holiday shopping (Black Friday anyone?).
- Unencrypted financial transactions: An easy way to check, is to look for the S in HTTPS, don’t enter your financial data into unencrypted websites.
Beyond attacks aimed at individuals, attacks aimed at businesses also tend to rise during the holidays and on weekends.
Such was the case for the attack on Kaseya, which occurred over Fourth of July weekend in 2021, and the Colonial Pipeline hack happened during Mother’s Day weekend the same year. Hackers realize there is less coverage on the weekend and during Holidays and they have taken advantage of it to great success.
It’s not just large businesses that are a target either, many wannabe hackers have day jobs too and more time on their hands during the holidays to target businesses that could be local to them. That includes yours.
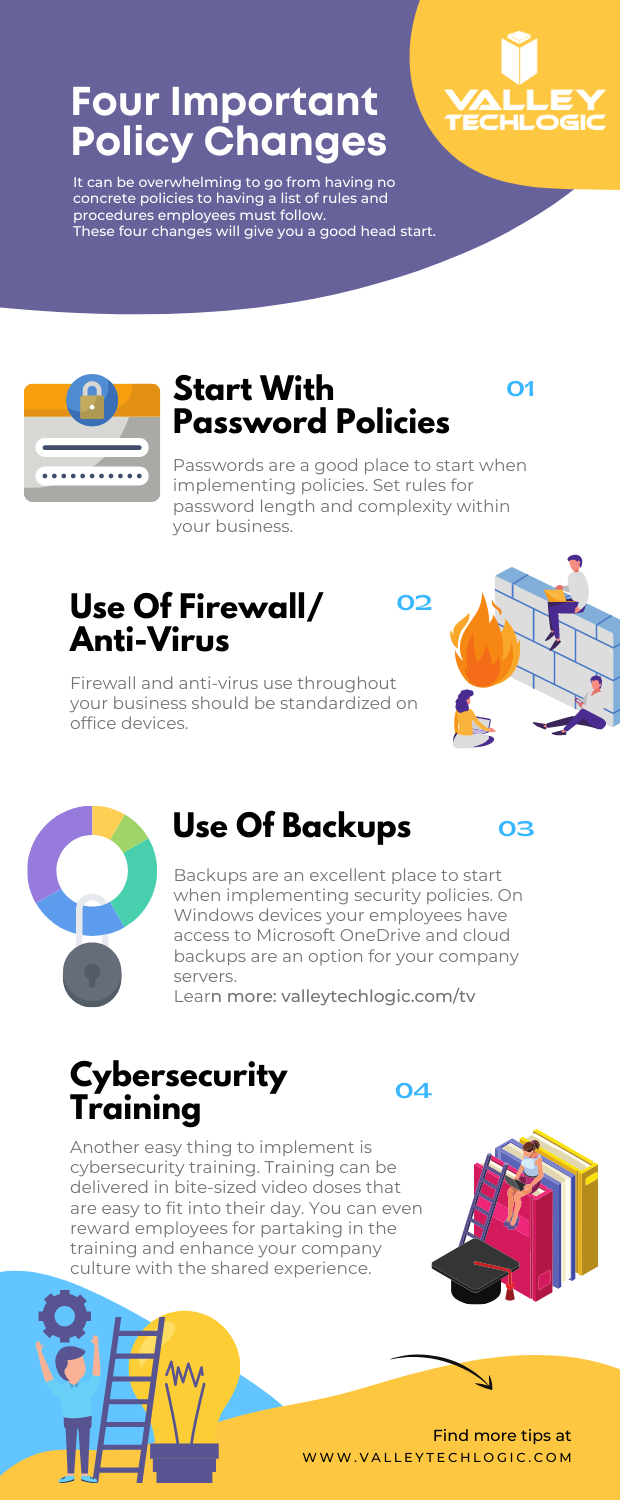
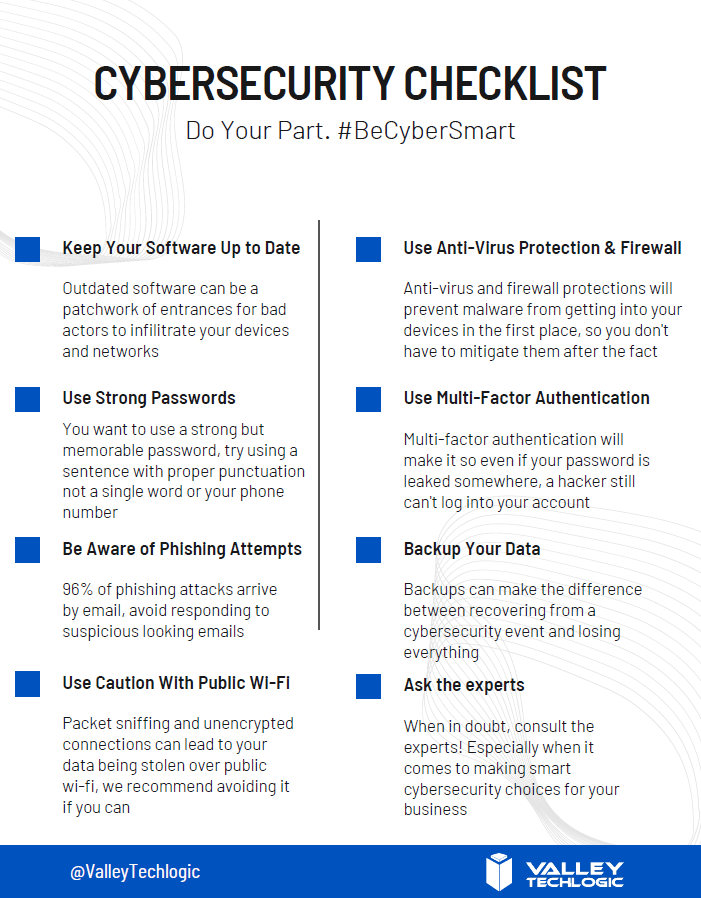
So, here’s a list of things to check off before you leave the office this week to enjoy some well deserved time off.
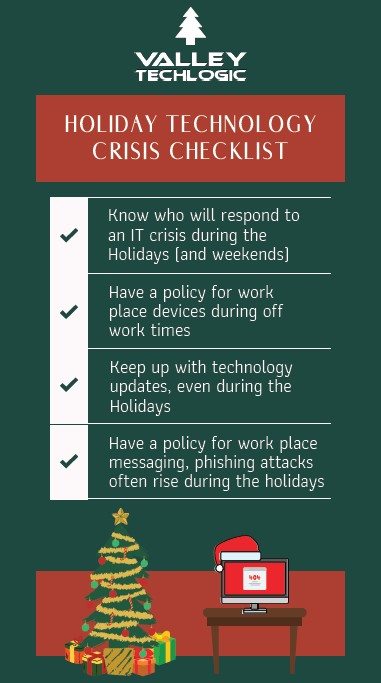
As you can see, our number one recommendation is knowing who is going to cover your business if a cyber event does happen while everyone is home for the holidays. If you try to think of who that person is and you either come up empty or maybe it’s you, that’s a problem.
Another problem is if your normal IT coverage is on a one time or break fix solution basis. The service you normally use could either be too swamped themselves to help you during the holidays, or maybe they’re taking time off too and are simply unavailable to help you.
This is where having a contract with a technology service provider could really save the day during a crisis. When you have a contract with a business to provide your technology services, they’re bound by the service level agreement (SLA) you sign at the start of service. They will be better equipped to help your business if there’s a crisis – even during the holidays.
If you’re in the Fresno, Modesto, Sacramento or anywhere else in the Central Valley and aren’t really sure who you would turn to if a technology crisis occurred during the holidays, Valley Techlogic is here for you. Learn more today.
Looking for more to read? We suggest these other articles from our site.
-
Yesterday, Facebook experienced their worst outage since 2008
-
Windows 11 is out, should you upgrade?
-
10 Common Tech Questions & Our No-Nonsense Answers
-
The average cost of hiring IT support staff examined
This article was powered by Valley TechLogic, IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.