We’ve posted about LastPass data breaches before but at that time it was purported to be a false alarm according to the company, the news on this most recent breach is that it’s real and that LastPass users should be concerned.
The data breach in question happened in August but LastPass is just now revealing the details on what was stolen and the scope of breach. At the time of the hack LastPass was again saying that it was a false alarm but that wasn’t true and “backup customer vault data” was accessed during the August incident.
This backup vault data included both unencrypted data such as website URLs and encrypted data such as website usernames and passwords. Having both details will allow hackers to easily put two and two together to access customer accounts.
With that said because the data for usernames and passwords is still encrypted LastPass has let customers know their data is still safe, as they say it can only be unencrypted with their unique encryption key that is derived from your master password. User master passwords are not accessible due to their “Zero Knowledge” architecture.
With this architecture no one, not even LastPass themselves, has access to a user’s master password. LastPass requires that master passwords be 12 characters long so even if the hackers who accessed this data attempt to brute force individual passwords it would still be difficult to impossible, with LastPass themselves estimating it would take “millions of years using generally-available password-cracking technology”.
LastPass users should still be on the lookout for phishing attempts in the upcoming days however, even if your data is safe bad actors may still use the news of this breach to attempt to trick users into revealing their data. You should never share your password details with anyone, especially your master password. LastPass will never ask you for your password information.
Also some additional advice for business owners who may own websites from Google, because the URLs in this breach were not encrypted they may include some that you didn’t want publicly accessible. John Mueller a SEO expert at Google recommends reviewing any website URLs you may have that may inadvertently leak data for your business, including customer form data.
We still believe password managers are a security benefit to both consumers and businesses alike. They’re one small part of increasing overall cybersecurity awareness and safety and fall under the larger spectrum of increasing user education and accountability.
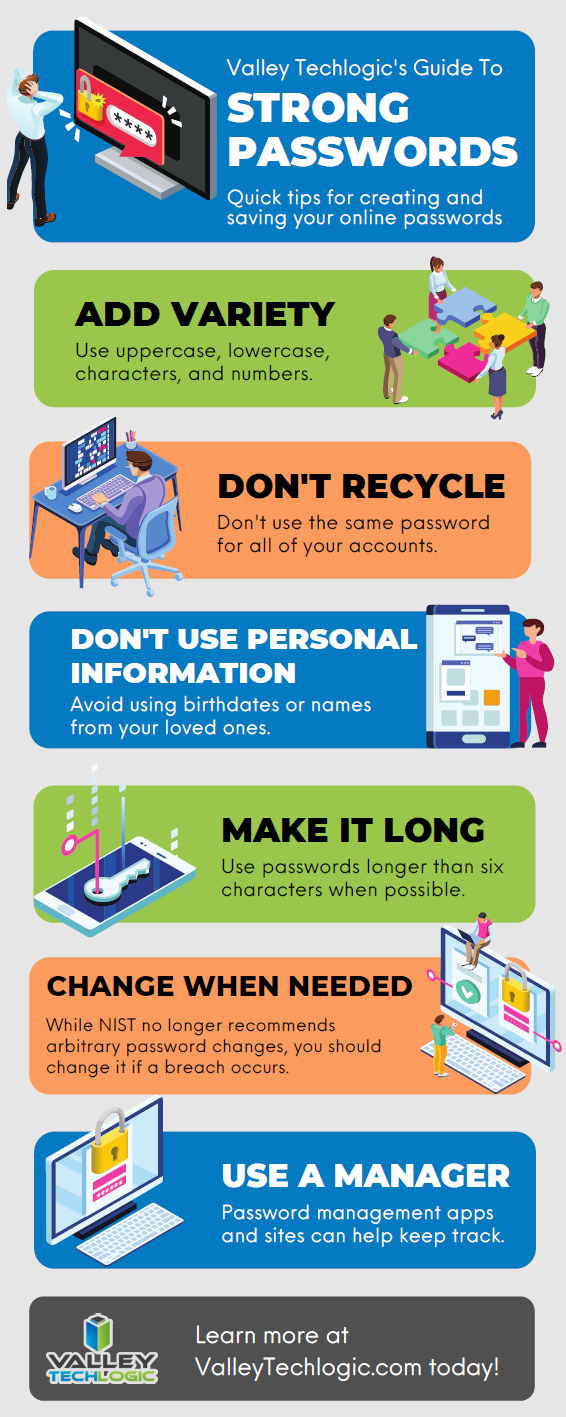
We’ve posted about proper password safety and advice on avoiding phishing attacks, but here are the top 5 things you can enable in your business today to improve your cybersecurity safety in 2023.
 If news of breaches make you nervous and you aren’t sure if your business is prepared from a cybersecurity standpoint, Valley Techlogic can help. We consider ourselves to be a premier provider of cybersecurity services for businesses in our area and beyond. We can help your business by covering your endpoints, setting up secure backups, virus and malware scanning and prevention and more. Schedule a consultation today.
If news of breaches make you nervous and you aren’t sure if your business is prepared from a cybersecurity standpoint, Valley Techlogic can help. We consider ourselves to be a premier provider of cybersecurity services for businesses in our area and beyond. We can help your business by covering your endpoints, setting up secure backups, virus and malware scanning and prevention and more. Schedule a consultation today.
Looking for more to read? We suggest these other articles from our site.
-
10 Holiday Shopping Tips for Safer Online Shopping
-
Thinking about buying new tech for your business in 2023? Here are our top 10 tips
-
High Tech Holidays – Five Ways Technology Can Make Your Holiday Season Easier
-
Hackers and the holidays, US government warns ransomware doesn’t take days off
-
Black Friday Isn’t just for consumer purchases, business owners can take advantage as well with these tech deals
This article was powered by Valley Techlogic, an IT service provider in Atwater, CA. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on Twitter at https://x.com/valleytechlogic.